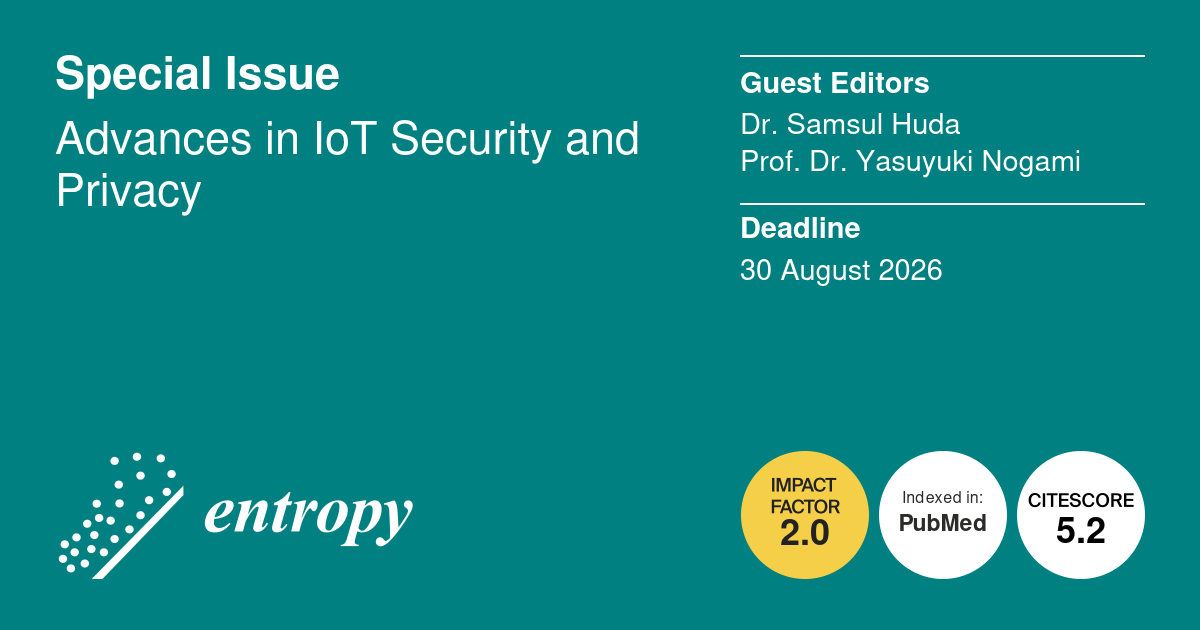
SI - Advances in IoT Security and Privacy - Entropy
Open submission
This Special Issue highlights highlights how information‑theoretic principles and entropy‑based methods address emerging vulnerabilities in IoT ecosystems.
Overview
Deadline: August 30, 2026
Guest editors: Dr. Samsul Huda and Prof. Dr. Yasuyuki Nogami
We welcome high-quality, original research articles, reviews, and case studies that use entropy, information theory, uncertainty quantification, or complexity-based approaches to advance IoT security and privacy. Topics of interest include, but are not limited to, the following:
- Information-theoretic cryptography and physical-layer security for resource-constrained IoT devices.
- Entropy-aware AI/ML methods for threat detection, including uncertainty quantification, information bottleneck optimization, and entropy-regularized learning.
- Domain-specific IoT security (e.g., healthcare, smart homes, industrial IoT) with formal privacy guarantees based on min-entropy, Rényi entropy, or differential privacy.
- Security architectures and trust models grounded in information flow analysis, mutual information bounds, or entropy-driven risk assessment.
- Blockchain and decentralized consensus mechanisms for IoT, analyzed through entropy-based metrics of fairness, randomness, or information dissemination
- Secure and verifiable firmware/software updates using entropy-based integrity fingerprints or randomness extraction from device behavior.
- Intrusion detection and anomaly identification based on statistical entropy, Kolmogorov complexity, or stochastic deviation from normal operational states.
- Privacy-enhancing technologies (PETs) with quantifiable information leakage limits, including entropy-minimizing data sanitization and obfuscation strategies.
- Real-world case studies that empirically evaluate security or privacy in IoT systems using information-theoretic metrics (e.g., entropy of sensor data, mutual information between attack signals and system responses).
More detail and submission: https://www.mdpi.com/journal/entropy/special_issues/5Z18Q6TYDE/.