Research
Interests
Network Security Internet of Things (IoT) Computer Networks
Topics
Intrusion Detection in Agricultural IoT Networks
Green By Digital (GYD) Projects
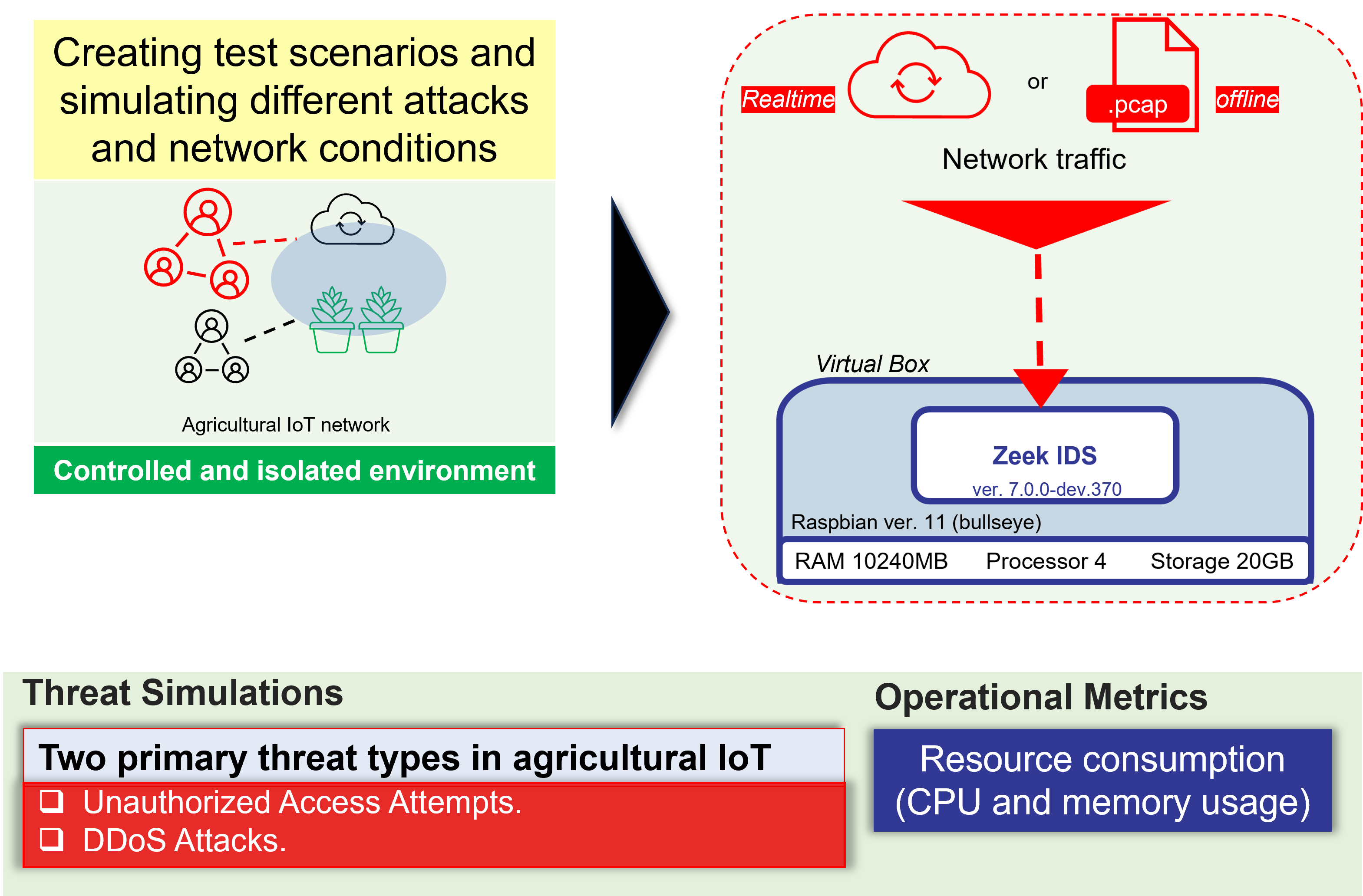
The increasing adoption of IoT technologies in agriculture has transformed crop monitoring and management practices. However, as agricultural networks become increasingly connected, they also become potential targets for cyber threats. These threats pose significant risks to the security and integrity of farming operations. We explore the potential of Zeek, an open-source Network Intrusion Detection System (NIDS), in securing IoT devices within agricultural scenarios. We deploy Zeek in a Raspberry Pi virtual environment using VirtualBox, as it provides a controlled and isolated testing environment.
Design of Blockchain-Based Secure Device Authentication for IoT Plant Monitoring Systems
Green By Digital (GYD) Projects
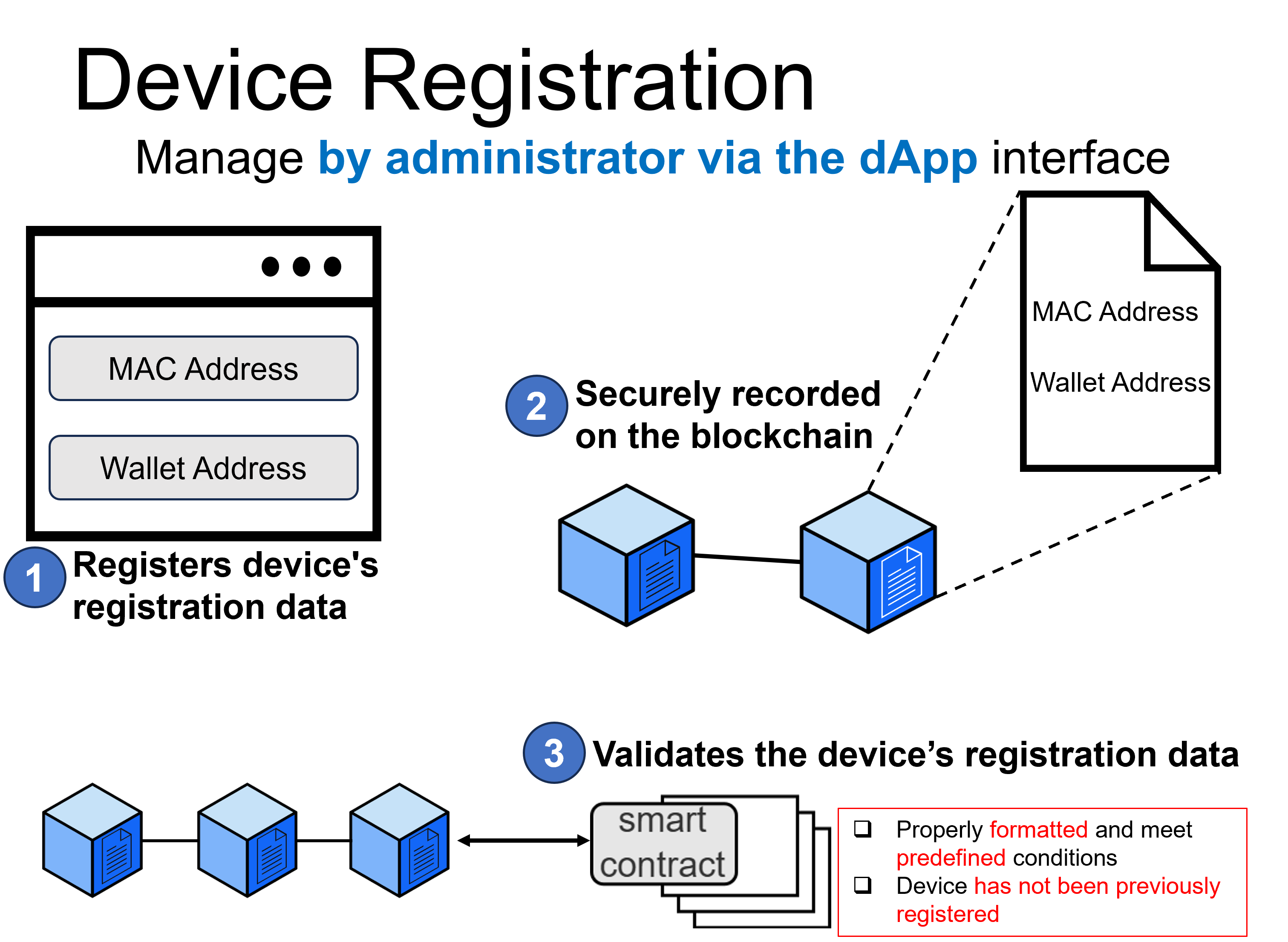
The adoption of Internet of Things (IoT) devices in agricultural applications, such as plant monitoring systems, has been growing. However, these devices are often untrusted, and malicious nodes may inject bad data. Blockchain (BC) technology can address this issue by ensuring the immutability and transparency of IoT interactions, thus preventing unauthorized access and transactions. In this study, we present a design for secure device authentication to connect IoT devices to decentralized application (dApp) using blockchain, specifically within a plant monitoring system. Our design includes two key processes: device registration and authentication.
Secure Authentication for Plant Monitoring System Sensor Data Access
Green By Digital (GYD) Projects
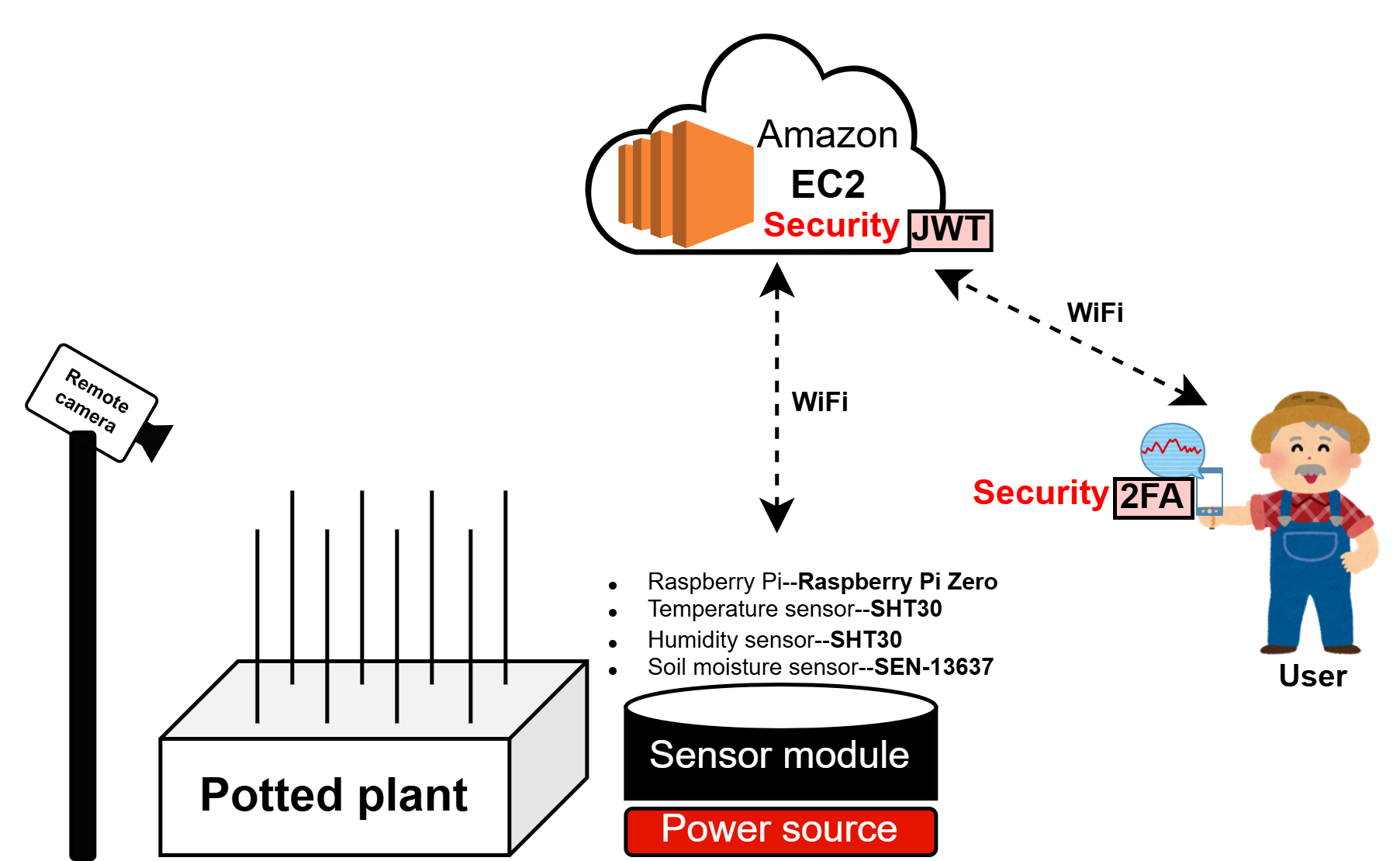
The previous IoT agriculture application implemented a login system and token‑based authentication to enhance security. However, it may still introduce potential vulnerabilities, such as the risk of password interception due to the inherent insecurity of using HTTP for data transmission in the development environment, as well as issues arising from tokens that do not expire. To address these security concerns, we propose secure authentication for accessing the plant monitoring system’s sensor data. The proposed solution incorporates two-factor authentication (2FA) and JSON web tokens (JWT) approaches to enhance security.
AgriDX: IoT Application for Plant Monitoring System
Green By Digital (GYD) Projects
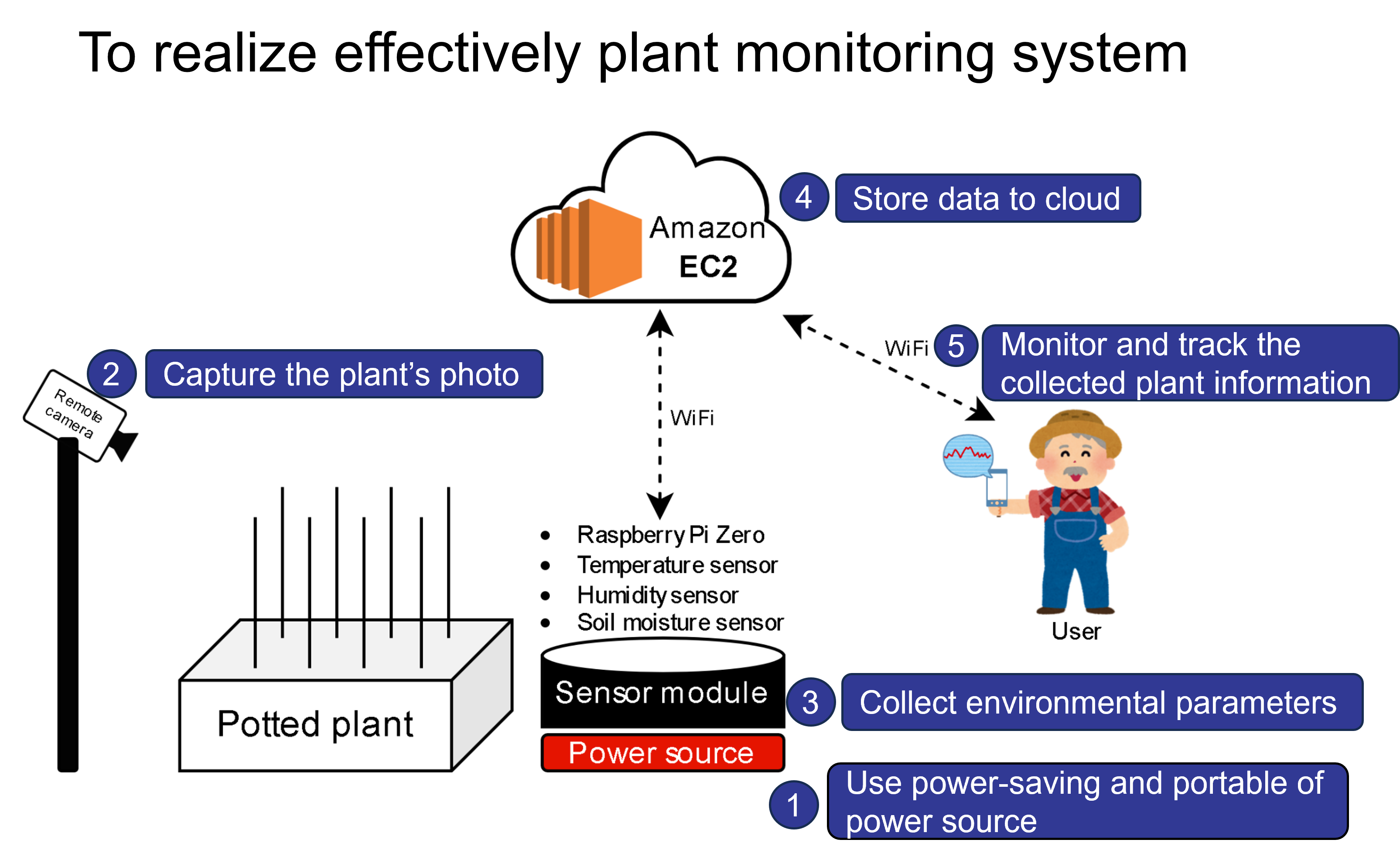
To encourage effective monitoring in plant agriculture, we present an Internet of Things (IoT) application for plant agriculture monitoring systems to help farmers monitor and track plant environmental conditions. The system consists of a remote camera, power source, a sensor module, and an AWS cloud platform. To reduce power consumption, it periodically measures various environmental parameters such as temperature, humidity, and soil moisture with power management configured.
Air-Conditioning Guidance System
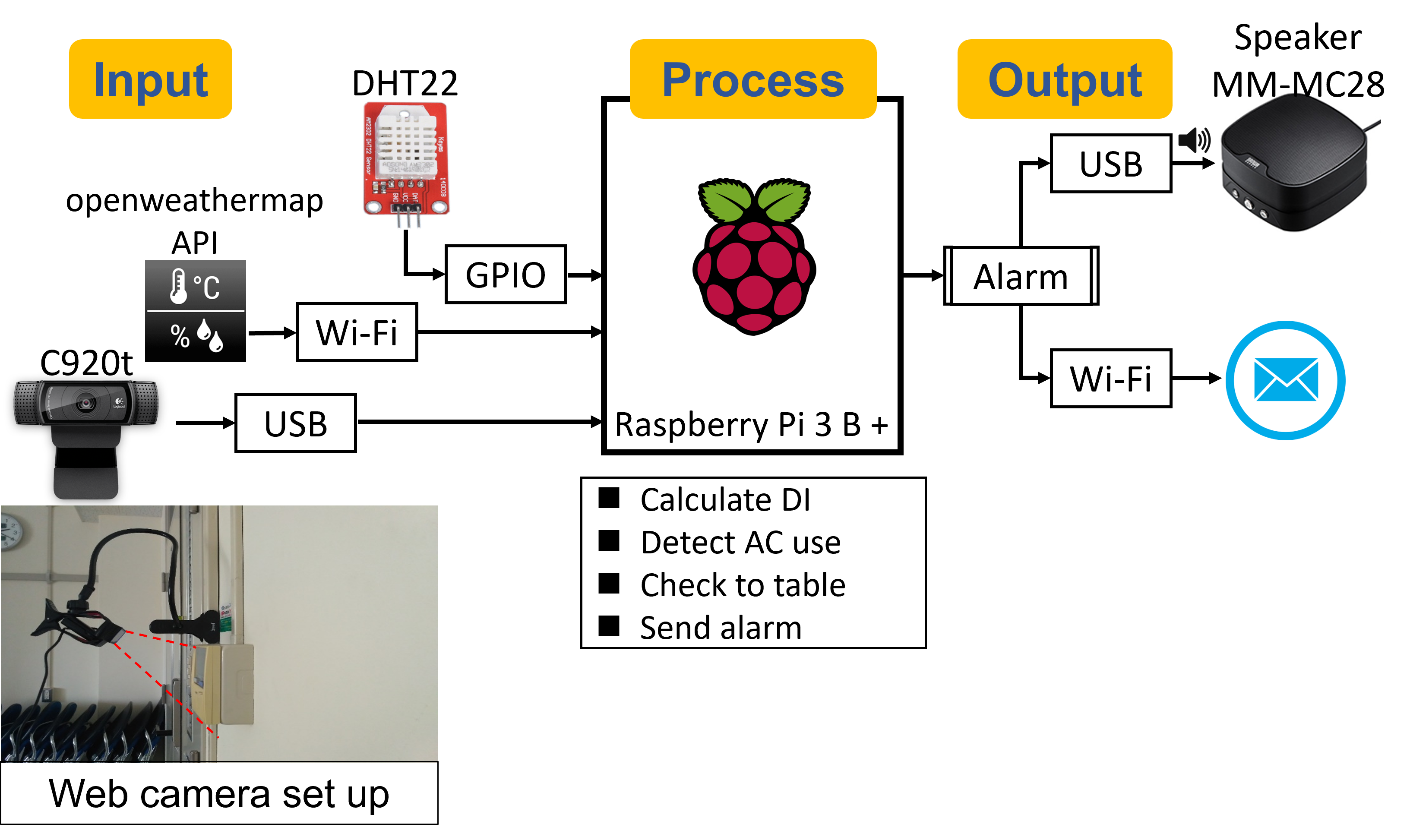
This air‑conditioning guidance system (AC‑Guide) is designed to encourage proper and optimize use of air‑conditioning. Air conditioners are often overused or underused because indoor temperature adjustments are made without considering outdoor conditions. For example, if the weather outside is cool, the AC should be turned off and the windows opened. Conversely, if the outdoor temperature is high, the AC should be turned on. This system periodically, 1) samples the temperature and humidity of the room with the sensor, 2) obtains the outdoor weather data from an API, 3) calculates the discomfort index (DI) for the indoor and outdoor, 4) detects the on/off state of the AC using the image, and 5) sends a message of requesting turning on/off the AC when the DI is outside/inside the comfortable range.
Calligraphy Learning Assistant System
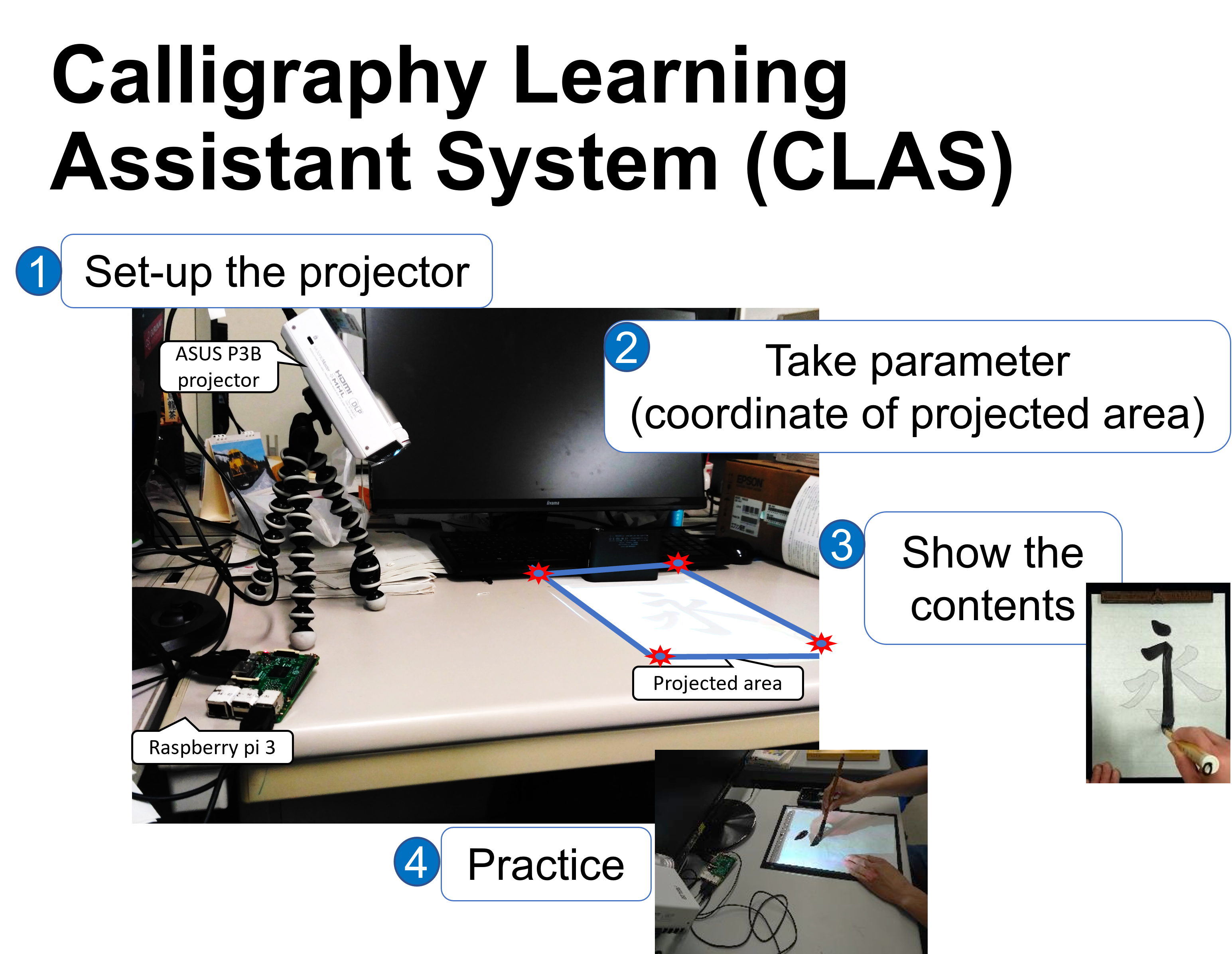
This calligraphy learning assistant system (CLAS), which uses projection mapping, is designed to support self‑learning of calligraphy. This system allows self-learning of calligraphy while imitating the stroke order and speed of a teacher through: 1) recording the writing of a teacher, 2) converting it to projection mapping, and 3) practicing writing by following the movie projected on the paper. By tracing the teacher’s projected writing, learners can acquire not only the correct letter shapes but also the appropriate stroke order and writing speed. In addition, the system includes a letter‑portion practice function that allows learners to repeatedly practice difficult parts of each character.
Secure Data Sensor Sharing in Environmental Health Monitoring Application
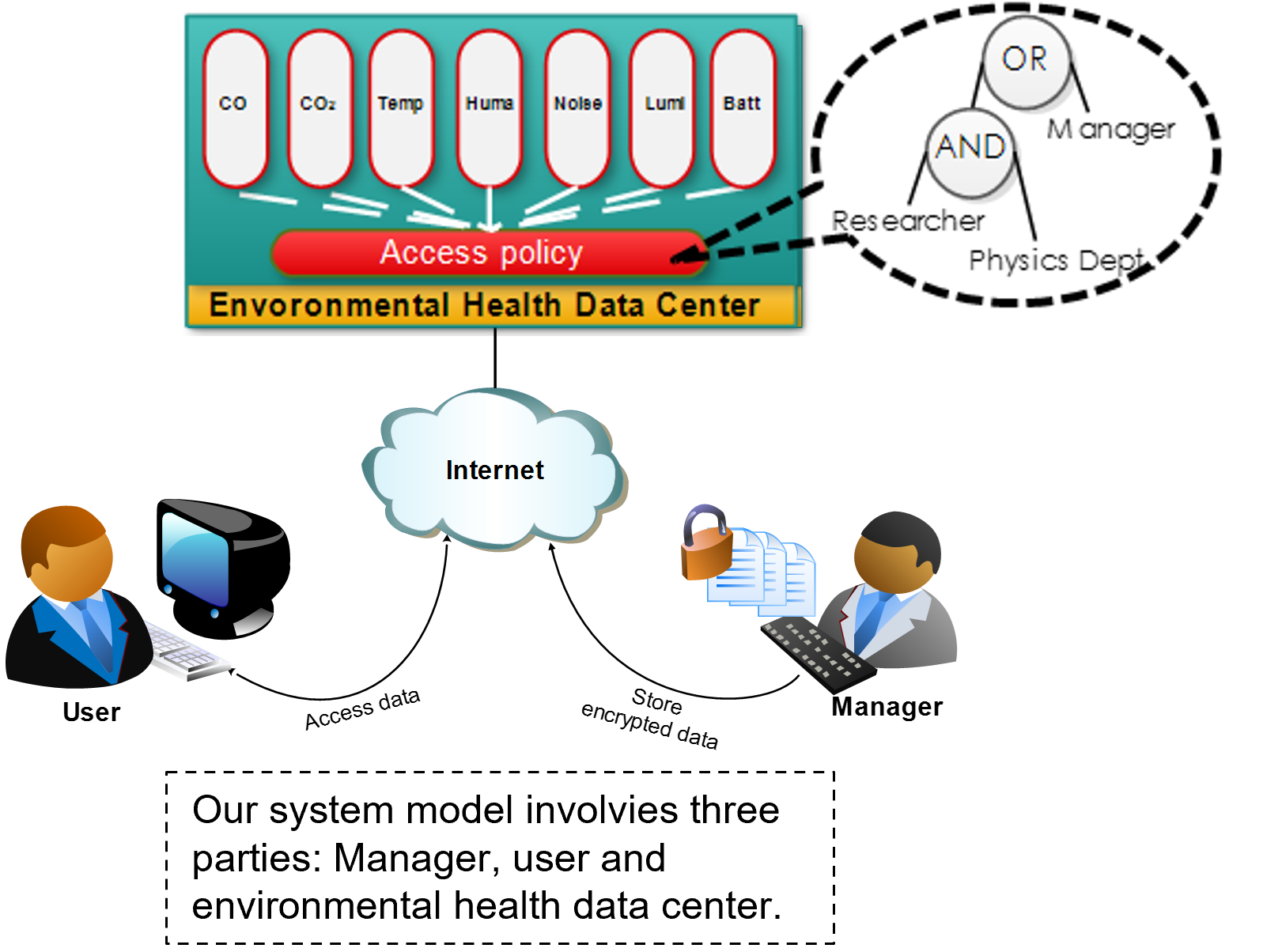
In environmental health monitoring systems, data stored in the data center must be accessible from various user devices at anytime, while ensuring secure access. Only authorized users should be able to retrieve sensor data from the environmental health data center. CP‑ABE (Ciphertext‑Policy Attribute‑Based Encryption) offers a robust cryptographic solution to address this requirement. To enable secure sensor data sharing and controlled access, we propose secure data sensor sharing using CP-ABE by present two protocols, registration and data sharing protocol, and various rules access policy for each sensor groups such as temperature, humidity, luminosity, noise, carbon dioxide (CO2) and carbon monoxide (CO) to ensure confidentiality, integrity, and user privacy aspects.
Authenticated Ciphertext Policy Attribute-Based Encryption in Mobile Ad-hoc Network
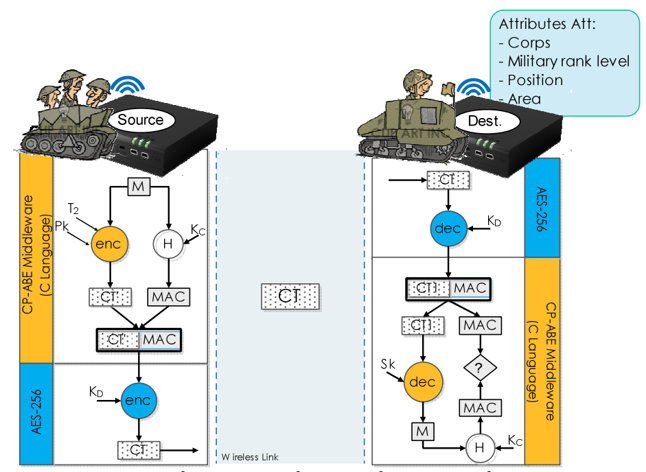
MANETs play a critical role in military operations, where high mobility, flexibility, and communication in open, uncontrolled environments are essential. However, operating in such conditions exposes MANETs to various attacks, including packet eavesdropping, data dissemination, message replay, message modification, and privacy breaches. In this paper, we propose a secure communication and information exchange in MANET with considering secure adhoc routing and secure information exchange. Regarding privacy issue or anonymity, we use a reliable asymmetric encryption which protecting user privacy by utilizing insensitive user attributes as user identity, CP-ABE (Ciphertext-Policy Attribute-Based Encryption) cryptographic scheme.
E-Commerce Security System using Schnorr Digital Signature Algorithm
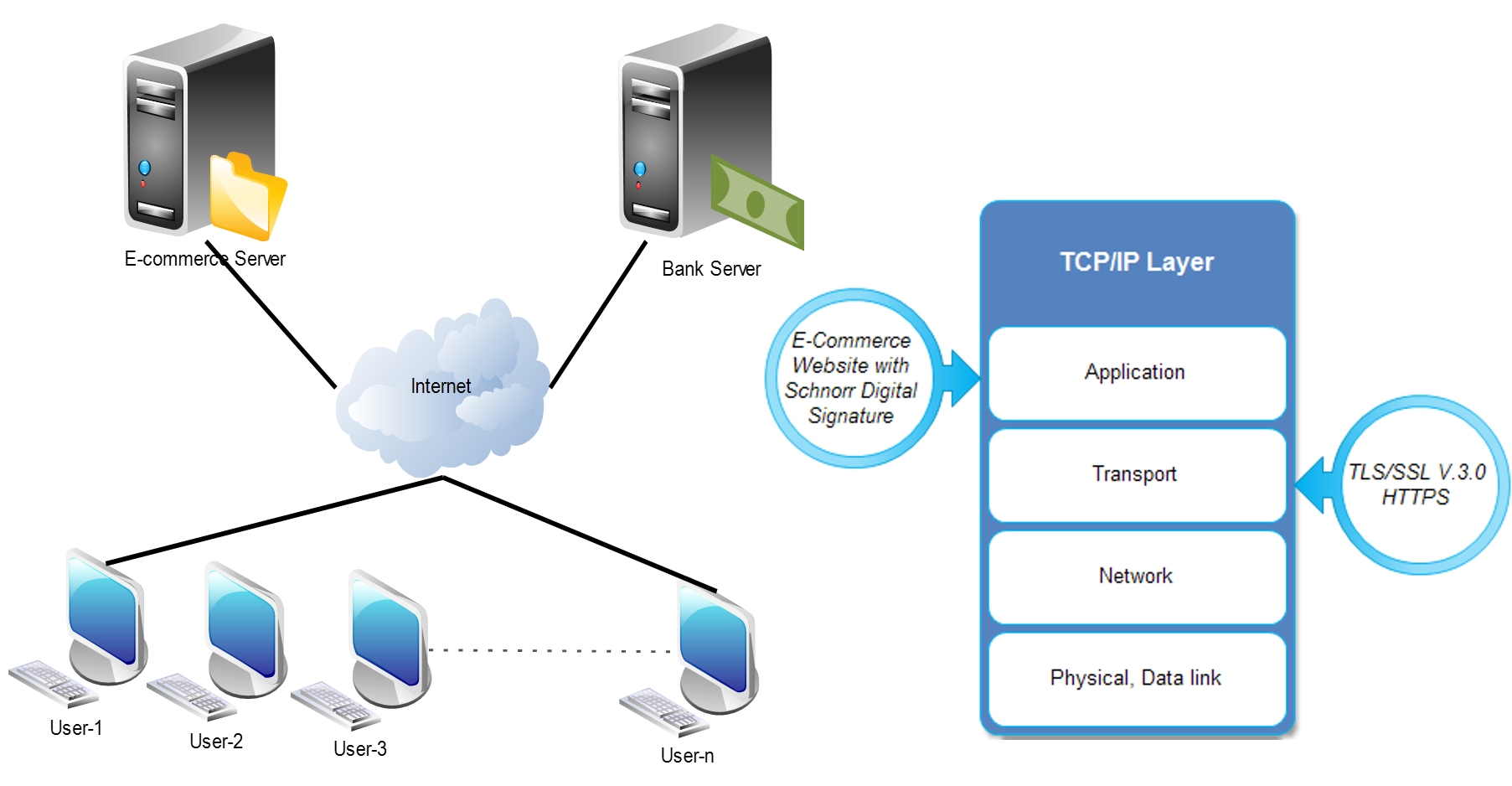
Secure transaction processing is a critical requirement in modern e‑commerce systems, where user authentication and data integrity must be guaranteed throughout online interactions. To strengthen protection at the application layer, this work implements the Schnorr Digital Signature Algorithm, providing lightweight yet reliable user authentication and message integrity verification. In addition, the system employs SSL/TLS (HTTPS) at the transport layer to secure communication channels and prevent interception or tampering during data transmission.